About Us
Services arrow_drop_down
Our Services
From secure identity management to robust web applications, we deliver solutions that protect, connect, and support your growth.
Identity and Access Management (IAM)
Empower your organization with innovative identity management solutions designed to secure access and streamline operations.
Software Development
Secure, scalable software tailored to your business goals—from web platforms to mobile apps and automation systems.
System Integration Services
Unify your tools and automate your operations with integration solutions built for speed, accuracy, and growth.
Portfolios arrow_drop_down

Our Portfolios
Explore our diverse portfolio of projects that bring security, scalability, and innovation to life across industries.

MyCoachingTree
Developed a centralized SSO authentication system for MyCoachingTree’s platforms, integrating SmartJobBoard and MightyNetworks with Keycloak.
arrow_right

ADRA
Reduced login friction and boosted efficiency for ADRA by integrating critical platforms and enabling secure Single Sign-On using Keycloak.
arrow_right
Case Studies arrow_drop_down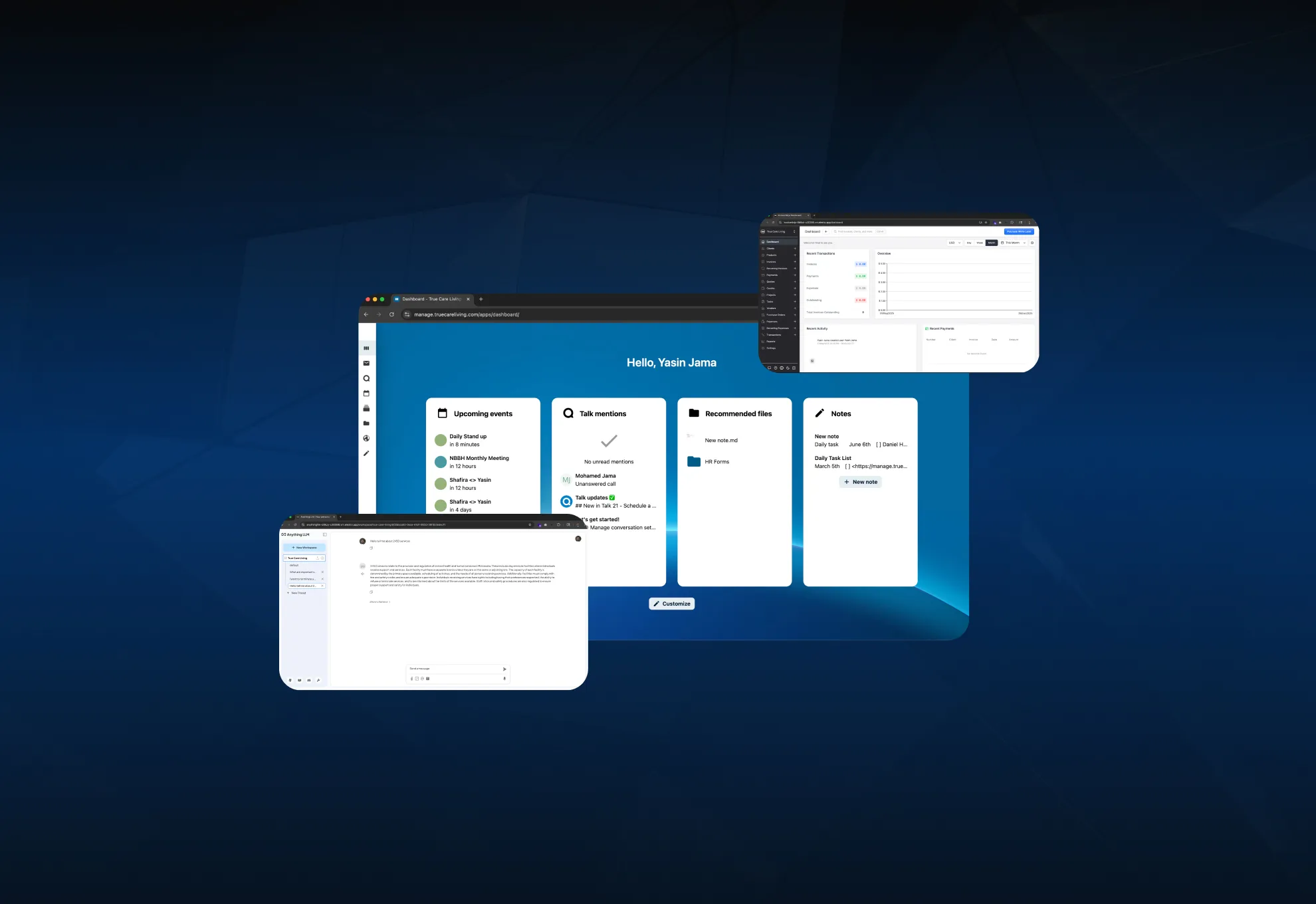


Our Case Studies
Explore how we solve complex challenges across industries, delivering secure, scalable solutions that make a measurable impact.
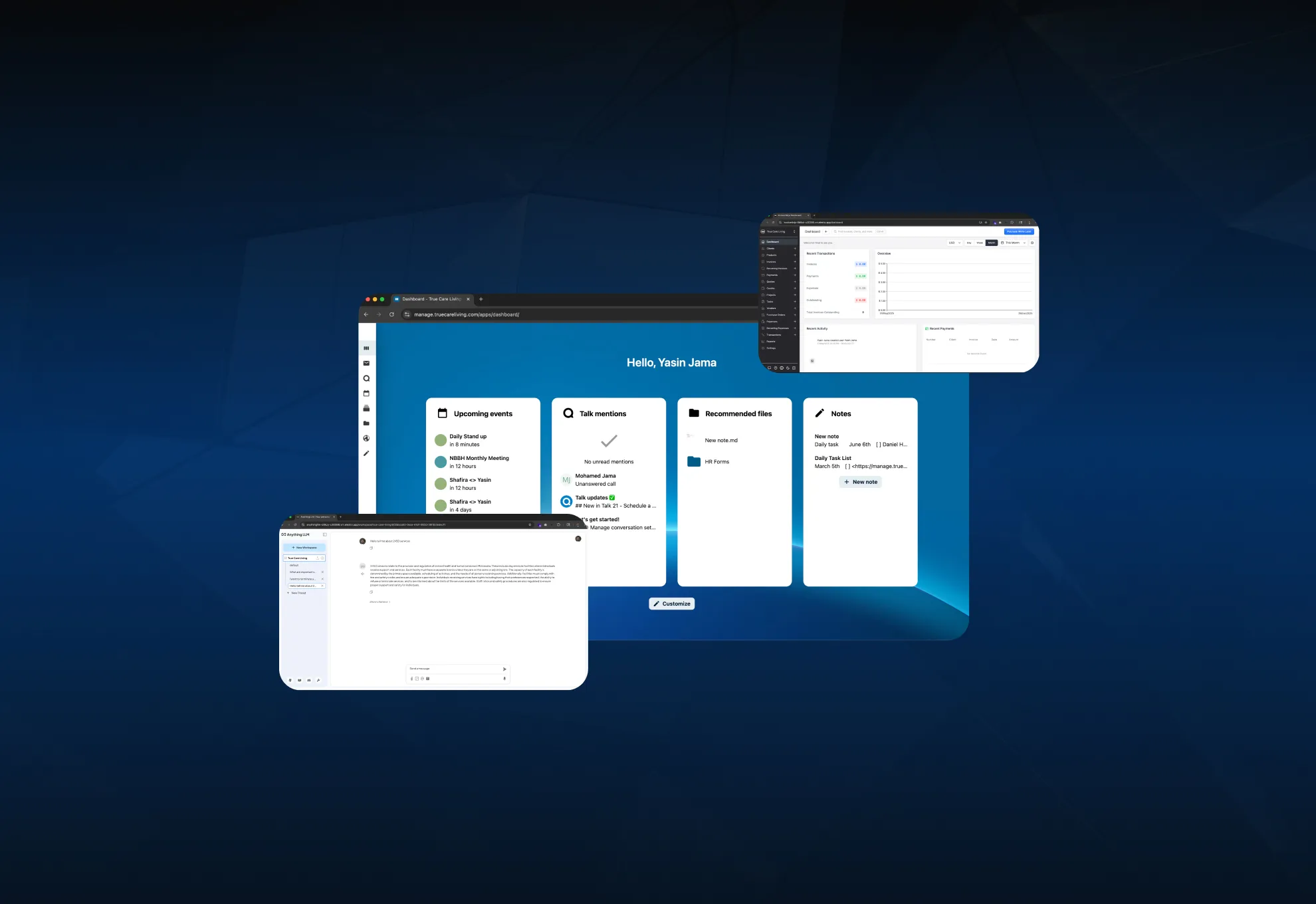
Future-Proofing Healthcare Operations with Open, Secure, AI-Ready Infrastructure
We helped True Care Living replace legacy systems with a secure, open-source document platform that’s fully integrated and AI-ready.
arrow_right

Building a Scalable, HIPAA-Compliant Software Suite for the Homecare
Explore how Blue Horn Tech developed an end-to-end homecare software solution with mobile apps for caregivers and patients, and a secure admin web portal. From strategy to QA, we built a HIPAA-compliant platform that powers seamless scheduling, billing, EVV, and real-time care coordination.
arrow_right

Unifying Platforms and Securing Access Across a Global Nonprofit
This in-depth case study shows how Blue Horn Tech partnered with ADRA International to unify identity access, implement Keycloak SSO, and integrate over 15 digital tools. The result: stronger security, smoother operations, and a scalable digital foundation for global impact.
arrow_right
menu
Company
@2025 Blue Horn Tech, Inc. All rights reserved.